1. Kali on the Raspberry Pi
If you want a cheap and portable hacking platform to do some penetration testing of a network then loading Kali Linux on the Raspberry Pi is not a bad option. The caveat is that penetration testing can be quite processor intensive so for some activities, the Raspberry Pi will struggle (even using version 3).
The Kali version of Linux is a Debian-derived distribution designed for digital forensics and penetration testing. It is maintained and funded by Offensive Security Ltd. With its security toolkit you can crack Wi-Fi passwords, create fake networks, and test other vulnerabilities.
2. Installing Kali on a SD card (Using MacOS)
- Download the Kali Linux Raspberry Pi image for your hardware and unzip the .img file inside. Note: If you’re not using the touch screen display, download the regular version of Kali Linux for the Raspberry Pi.
- Download RPi-sd card builder (be sure to pick the appropriate version for your installed version of OS X) and unzip the application.
- Insert your SD card into your Mac using a card reader.
- Open RPi-sd card builder. You’ll immediately be asked to choose a Raspbian image. Choose the .img file you downloaded earlier.
- You’ll be asked if your SD card is connected. Since we inserted it earlier, it is, so go ahead and click Continue. You’ll be presented with SD card options. If you only have one inserted, you won’t see anything else in the list and it’ll be checked. If not, just check only the card you want to use and click OK.
- Enter your administrator password and click OK.
- You’ll be asked if the SD card was ejected. This is supposed to happen, as the application needs to unmount it so it can perform a direct copy. Double-check that your SD card is no longer available in the Finder. DO NOT remove it from your USB port. When you’re sure, click Continue.
- RPi-sd card builder finishes prepping your SD card, safely eject it and insert it into your Raspberry Pi unit.
3. WiFi Penetration Test
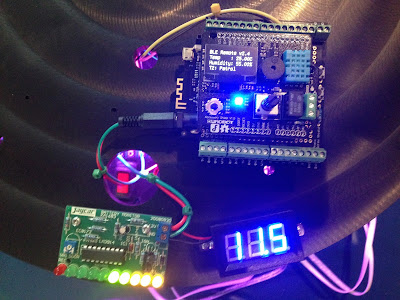
The picture above shows Kali running on my Raspberry Pi. To test out the functionality we will test the security of our WiFi network. Once you have performed this exercise you will be convinced of the need for a secure WiFi password! Cracking a WiFi network with WEP encryption is no challenge and realistically most WiFi networks will now use WPA (as ours does), so that will be the challenge.
Step 1 - Determine the name of your WiFi interface.
To do this type airmon-ng. This program is part of the Aircrack-ng package which is included in Kali. Airmon-ng places the WiFi interface into monitor mode.
Aircrack-ng is a network software suite consisting of a detector, packet sniffer, WEP and WPA/WPA2-PSK cracker and analysis tool for 802.11 wireless LANs. It works with any wireless network interface controller whose driver supports raw monitoring mode and can sniff 802.11a, 802.11b and 802.11g traffic.
As shown in the image below, the WiFi interface name on our Raspberry Pi is wlan0.
Once you have the interface name, you type airmon-ng start wlan0 (from here on replace wlan0 with the name of your WiFi interface). This will indicate any processes that may interfere with the WiFi scanning software. In addition it will place your WiFi interface into monitor mode. The new interface name will be wlan0mon. You can run airmon-ng again to check this.
Step 2 - Use Packet Sniffer to capture WiFi details.
The packet sniffer provided with Aircrack-ng is called airodump-ng. To use it, type airodump-ng wlan0mon. Note that we are analysing the network using the monitored interface.
The packet sniffer will immediately start capturing and displaying packets (image above). Type CTRL c when you want to stop airodump-ng. Airodump-ng will display a list of detected access points, and also a list of connected clients (“stations”). The first line shows the current channel, elapsed running time, current date and optionally if a WPA/WPA2 handshake was detected. Note that encryption for our access point is WPA2.
The information that we need to record is as follows:
- Channel (CH) = 6
- MAC address (BSSID) of the Access Point = 2C:30:33:27:4E:BE
To limit the data capture to a single Access Point (AP) that you are interested in, include the “- -bssid” option and specify the AP MAC address. For example: airodump-ng -c 6 --bssid 2C:30:33:27:4E:BE -w airdump.txt. The output of the scan will be placed in airdump.txt.
Step 3 - Determine the MAC address of the Raspberry Pi WiFi interface
This MAC address is required for Step 4 - the deauthentication attack. There are a number of ways to determine the MAC address of the WiFi interface of the Raspberry Pi. You could check the connections to the router or type ifconfig wlan0mon, but we will use a linux utility called macchanger since this can also be used to change your MAC address should this be required. The command to determine your current MAC address is macchanger - s wlan0mon. The results are shown in the image below. You need to record:
- MAC address of the Wifi Interface (Client) = 40:A5:EF:05:5E:DF
As an aside, if you do want to change the apparent MAC address of your Penetration Testing rig, the process is:
- Turn off the network interface: ifconfig wlan0 down
- Use macchanger to randomly generate new MAC address and assign it to the wlan0 network interface: macchanger -r wlan0
- Re-enable the network interface: ifconfig wlan0 up
Step 4 - Deauthentication Attack.
This attack sends disassociate packets to one or more clients which are currently associated with a particular access point. Disassociating clients can be done for a number of reasons:
- Recovering a hidden ESSID. This is an ESSID which is not being broadcast. Another term for this is “cloaked”.
- Capturing WPA/WPA2 handshakes by forcing clients to reauthenticate
- Generate ARP requests (Windows clients sometimes flush their ARP cache when disconnected)
Aireplay-ng is used to inject frames and is the tool used for our deauthentication attack. Aireplay-ng implements 10 different attacks:
Attack 0: Deauthentication
Attack 1: Fake authentication
Attack 2: Interactive packet replay
Attack 3: ARP request replay attack
Attack 4: KoreK chopchop attack
Attack 5: Fragmentation attack
Attack 6: Cafe-latte attack
Attack 7: Client-oriented fragmentation attack
Attack 8: WPA Migration Mode
Attack 9: Injection test
We will demonstrate the first one, deauthentication. To capture WiFi handshakes, the command is of the format: aireplay-ng --deauth 1 -a [AP MAC] -c [CLIENT MAC], so for our example the command looks like: aireplay-ng --deauth 1 -a 2C:30:33:27:4E:BE -c 40:A5:EF:05:5E:DF
Note that AP MAC comes from step 2 and AP CLIENT comes from step 3. This program can take a while to run.